Newest Java Update Fails to Protect Against Biggest Threat
Java vulnerabilities are still the number one exploit path to compromise endpoints on an enterprise. And the latest release on Wednesday still doesn’t fix everything. And unless you are running Invincea, a browser and system wrapper that prevents local exploit, you would be better off uninstalling java for now.
From the Reg here:
Apple released a Java update on Wednesday but it does not tackle a high-profile flaw that has become the target of attacks over recent weeks.
Java for OS X 2012-005 and Java for Mac OS X 10.6 Update 10 offer patched versions of Java for OS X Lion and Mountain Lion systems that tackle CVE-2012-0547. But this is a different beastie from the CVE-2012-4681 megabug currently stalking Java users, KrebsOnSecurity reports.
Oracle patched the CVE-2012-4681 megabug with an update to its vulnerable Java Runtime Environment (JRE) 1.7 last week. However Security Explorations, the firm that originally found the flaw, warned that the patch issued by Oracle was itself buggy, without going into details. Even the original flaw dates from April but people only really stood up and took notice after exploits began circulating, around two weeks ago.
The most straightforward advice in the midst of this confusion is for users to uninstall Java, or at minimum disable Java-related browser plugins
And what the hell is up with java always trying to install some third party app? At one point java tried to install Carbonite online backup. Today it tried to install the ASK toolbar- like another browser helper object is something people are clamoring for? Is Oracle really just sponsoring and monetizing their own security flaws?
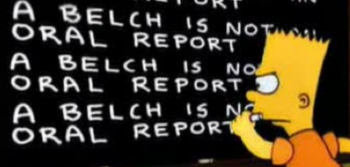
Every new Java update attempts to saddle my browser with the lame ASK TOOLBAR.Makes me think ASK is sponsoring all java flaws!
— Dr. Jones (@BelchSpeak) September 6, 2012