Solera Thinks Elmer Fudd is a Great Security Analyst
Solera is a deep packet inspection tool manufacturer. And while I firmly believe such tools are critical to perform security analysis, I wouldn’t let Shad Harris from Solera teach you how to use it. He posted a poorly written, rambling security blog at Solera which basically said that if you want to be a great security analyst, you have to think like Elmer Fudd. You have to be good at chasing “Wabbits”.
From SoleraNetworks here:
There is almost a frantic “chasing rabbits” game that most analysts play with their security tools. Granted not every incident is critically important but for the sake of my argument lets pretend this incident is “Defcon Red” level. The analyst begins a seemingly psychotic series of events in which they have to “check every rabbit hole over and over” knowing they will probably only find 1 instance of the infection that merits further actions.
It also helps to be familiar enough with the tool to make sure you can always “start over” if the investigation or drill down you just spent an hour on turns out to be a fruitless effort. Having the training to interpret the clues minimizes the wasted time/effort on the analysts’ part.
In summary, the incident response process is different for everyone. Sometimes completely unrelated life experiences or dispositions can lead to one analyst understanding more about a situation than another. Most times it boils down to training and experience, which we all agree is critical for all analysts. Some of the best Cyber security analysts have degrees in something completely unrelated to security, but because they put in the effort and time necessary to pick up the skill set they were able to impart that unique knowledge on an investigation and pick up the pieces quicker than “just the tools” would have allowed. Until the combination of life experience and training makes you a better analyst, it helps to be good at chasing rabbits.
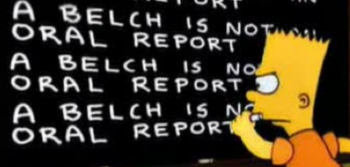
Shad Harris implies that his customers tend to be psychotically doing wrong things over and over, and with a blog post titled “Guide to being an analyst” he wildly misses the mark of any opportunity to impart any wisdom whatsoever. If I had to spend an hour using a deep packet inspection tool and kept coming up with zero results, I’d throw it out the window. The key to being a great security analyst is understanding your network and enterprise policy and monitoring for violations against it while also monitoring for things that should be prohibited by policy. That’s it. No life experiences required and certainly no “wabbits.”